Articles
Using captures in your StackStorm event driven automation
4 min read
StackStorm, by Extreme Networks, is a powerful automation platform that wires together all of your apps, services and workflows. It is richly extensible, letting you integrate with all manner of network equipment, analysis tools, and more. They have both an open source version and a version that is part of Extreme Networks’ “Extreme Workflow Composer”.
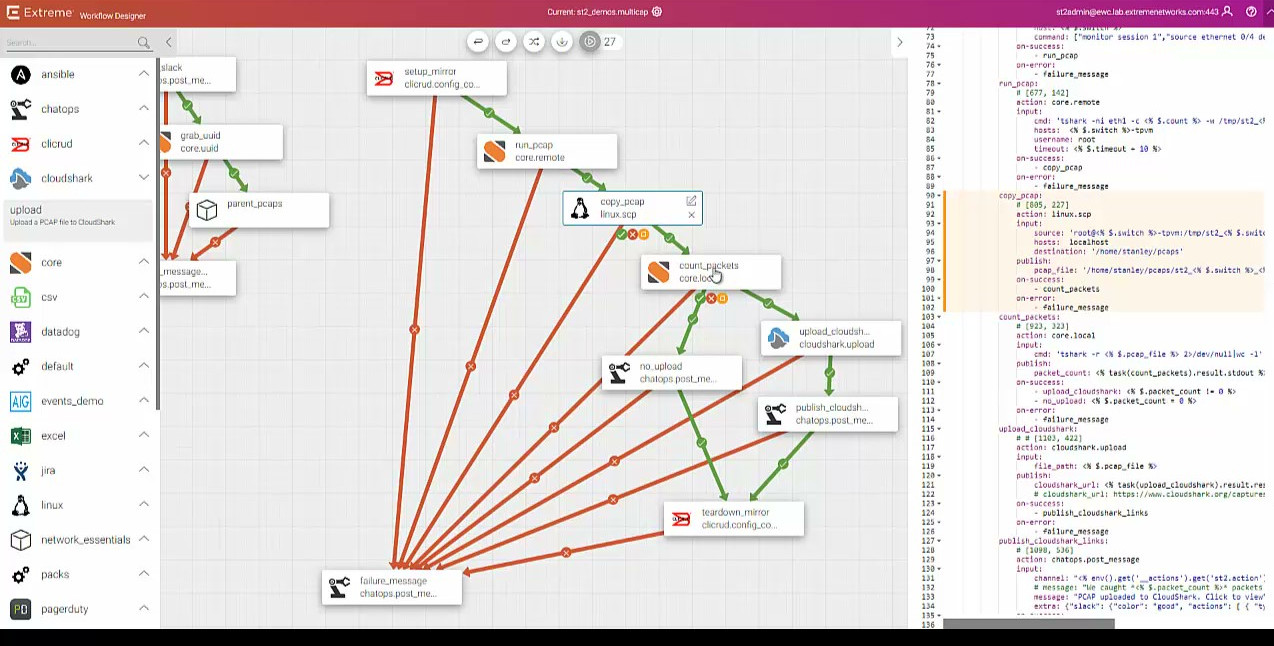
The team there has built a plug-in for CloudShark upload that they featured at Networking Field Day 17 (part of their StackStorm-Exchange open source projects). Example implementation You can see Lindsay Hill go through an example in the first half of this video. In the example, he’s built an automation flow in StackStorm that looks like this:
Example implementation
You can see Lindsay Hill go through an example in the first half of this video. In the example, he’s built an automation flow in StackStorm that looks like this:
Using capture software on a node
To get started, you’ll need to have the server or node where you want to capture have some capture mechanism like tcpdump or tshark.
Running a capture with StackStorm
Using StackStorm’s core.remote module, you can run any number of external commands on the node over SSH, including kicking off captures like these. Most capture tools let you stop capturing after a certain duration or after a certain number of packets have been captured, and you can set that up here as well.
Once the packet capture is complete, Lindsay’s flow moves the capture to a known directory (in this case, the home of the user that’s logged in) using the copy command from the linux module.
Uploading to CloudShark
After checking to see whether or not the capture is empty, the flow then calls the CloudShark module to upload to CloudShark through the CloudShark API. The flow then does some final cleanup of the resources built in the process (in this case, a port mirror was built in the beginning to grab a capture from a particular switch port).
Making this part of automation
StackStorm is an event driven automation system, so with this flow in place you could trigger the system to initiate a capture when a certain event is seen, then push the capture to CloudShark, getting an easily sharable URL for analysis as well as storing an tagging the capture for later investigation.
In the example above, the developers have integrated it with Slack, so the capture sequence could be kicked off by your DevOps or help desk folks as needed.
What do I do with my captures in CloudShark?
Pushing your captures from remote systems has a number of advantages.
Secure, store, and correlate historical data
With all of your captures in one place, you have a central repository of capture data that can be tagged based on events or trouble tickets. If you’re using CloudShark’s threat assessment tool, you can take Indicators of Compromise like IP addresses, known hosts, etc. and use DeepSearch to see if an attack goes back further than originally thought.
Merge captures from multiple sources
If you’ve triggered captures from more than one interface or locations, you can use CloudShark’s Merge Captures tool to build a single capture that has all of the packets together. You can then use CloudShark’s ladder diagrams to get a complete picture of protocol conversations over multiple endpoints.
Extract the data you’re looking for
If you’ve generated a pretty large capture using the StackStorm automation, sometimes finding an issue can be like looking for a needle in a haystack. If you have some idea of the endpoints, protocols, or other data you’re looking for, you can build a filter using standard Wireshark filters and then use the capture export feature to create a new capture containing only the information you need.
Work with capture data faster
With no need to install Wireshark on analyst’s systems, your team can jump immediately into problem solving. CloudShark’s web-based tools are easy to use, work with standard Wireshark filters, and can all be shared between people by passing around a URL. Even with captures in a data store, having to open Wireshark or another tool and explain how to get to the same view that you’re seeing can be tedious; URL based views let you do it all in one step.
Looking to integrate?
StackStorm’s integration is a great example of using our API to make working with captures easier. If you work with captures or produce a tool that works with them, let us know and we can help you build CloudShark into your workflow!